Operation GhostCargo
TLDR;
Identified a fraud activity with multi-stage phishing using courier-themed lure sites and bank-themed credential harvesting pages, likely powered by a reusable phishing kit cloned via HTTrack.
Phishing flow includes a fake CAPTCHA to filter bots and increase legitimacy, followed by bank impersonation pages designed to steal credentials and personal/ID information.
Courier websites are non-functional and fraudulent, with copied content, invalid contact details, broken tracking features, and links to other known scam domains.
The attack relies heavily on social engineering and trust-based pretexting, presenting a believable business transaction to manipulate victim behavior rather than exploiting technical vulnerabilities.
Attribution, delivery vector, and data exfiltration methods remain unconfirmed, but infrastructure patterns suggest a phishing‑as‑a‑service–style ecosystem with distributed, low-cost hosting.
This investigation identified a fraud activity comprises of multi-component phishing infrastructure with courier-themed lure websites, a CAPTCHA-based filtering layer, and banking credential harvesting pages. Evidence suggests potential use of a reusable phishing kit deployed across multiple domains, with structural similarities.
At this stage, analysis is limited to infrastructure and kit-level observations. The initial access vector, exfiltration endpoints, and attribution remain unconfirmed.
Analysis
The case study indicates that the phishing pages were delivered through social engineering. The threat actor engaged the victim with a fabricated business opportunity involving the purchase of industrial grade chemical products on their behalf. This tactic created a credible commercial setting that helped build trust and direct the victim to the phishing pages designed for information collection and potentially financial fraud.
Analysis of the observed dataset indicates that the phishing activity follows a multi staged approach designed to increase the likelihood of victim engagement. Two phishing pages observed are:
A bank-themed phishing page [bnk.ing-boa[.]pro]
A courier-themed phishing page [jetexpressdeliveries[.]com]
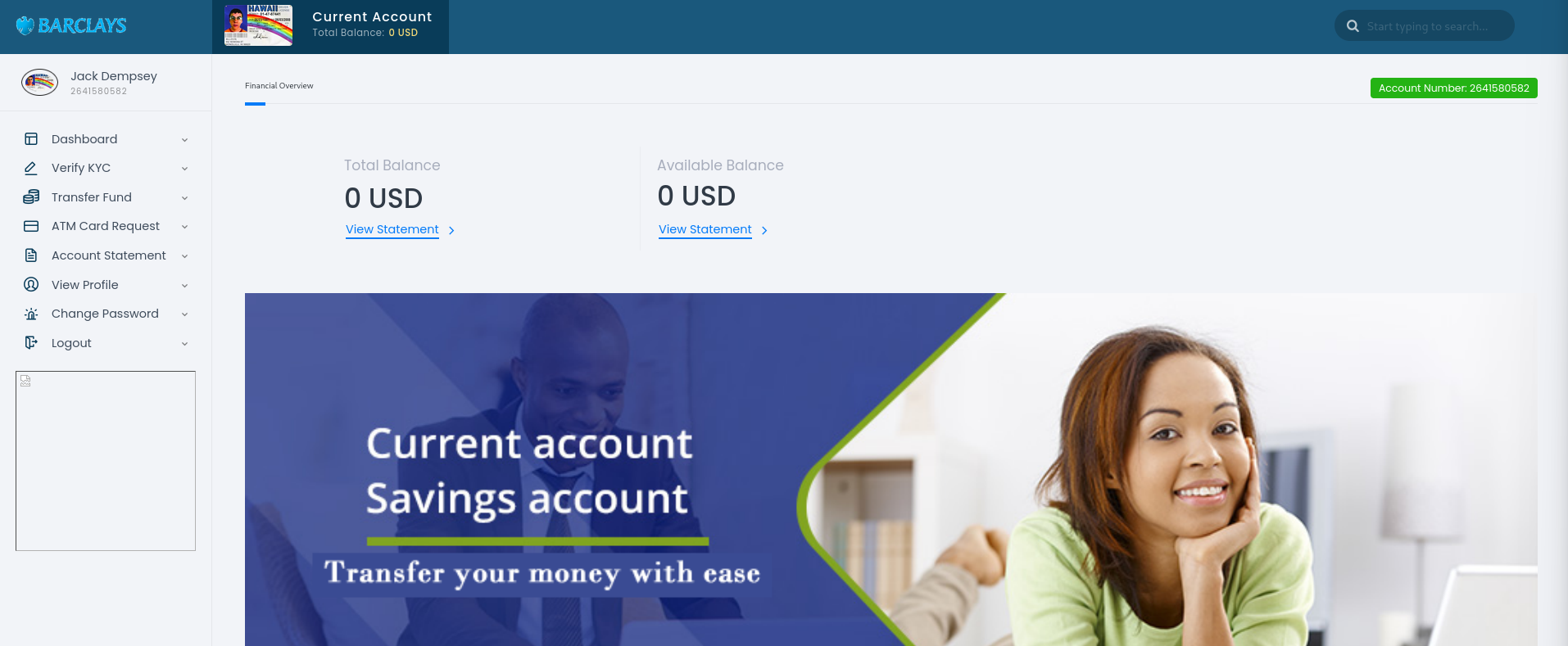
Barclays Bank impersonation page
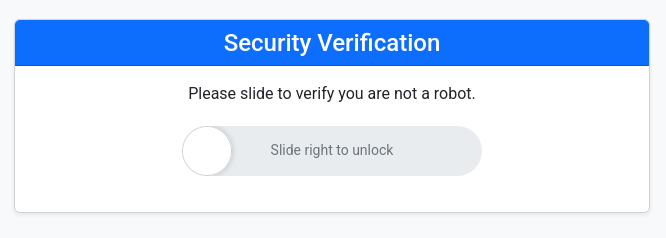
Visitors to the phishing page are first presented with a slider style CAPTCHA. While this feature appears to provide verification, no backend validation logic was identified in the current dataset. Its primary purpose is likely to filter simple automated bots, evade basic sandbox environments and increase the perceived legitimacy of the phishing page. This lightweight mechanism supports the threat actor’s effort to create a more convincing and controlled entry point into the phishing sequence.
Slide style CAPTCHA verification page
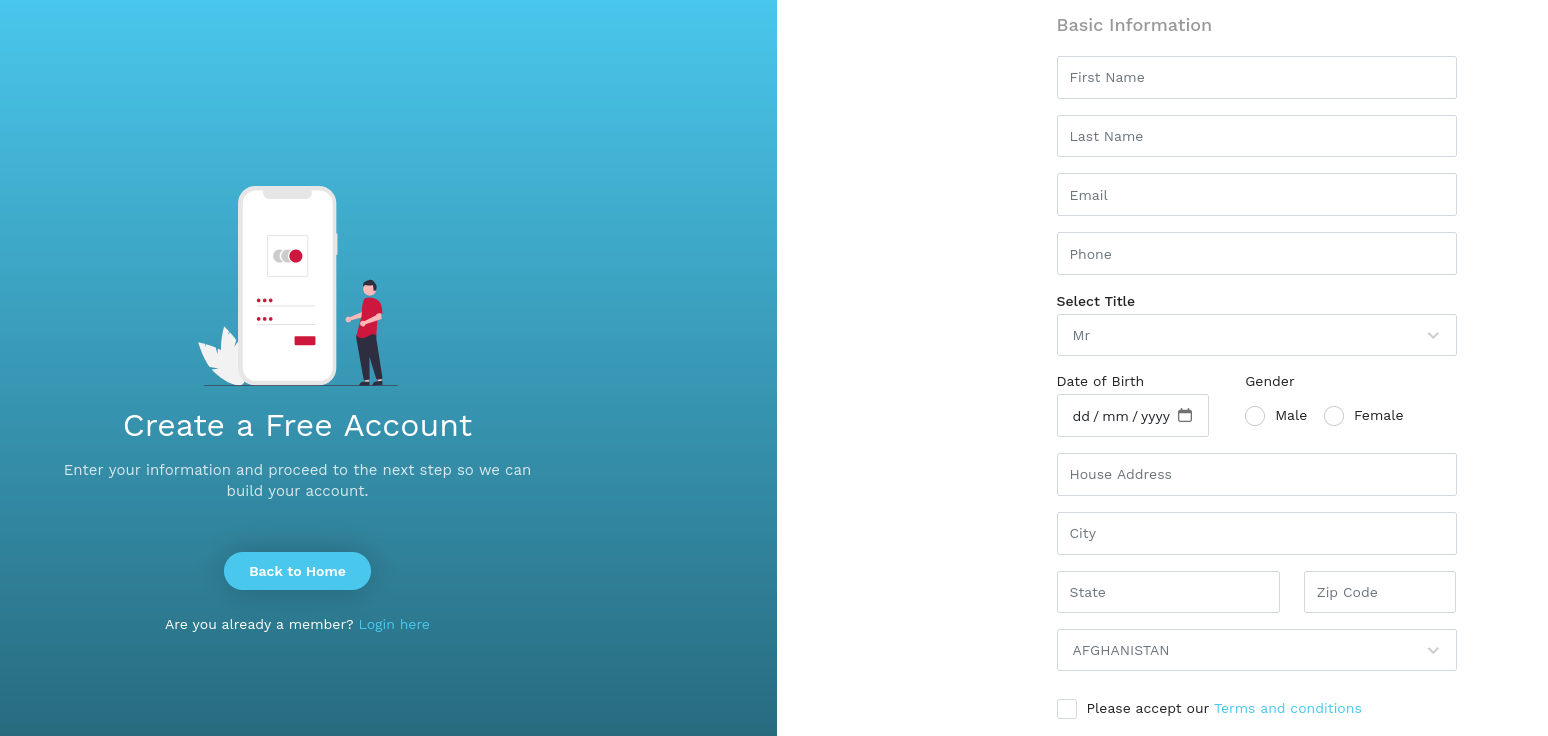
This phase directs the victim to sign in with their Barclays Bank credentials or create a new account if they do not already have one. The registration page is designed to harvest detailed personal information, including full name, phone number, email address and home address, along with an uploaded copy of an identity document such as a passport or identification card. After successful registration, victims are redirected to the login page.
The registration page
The user dashboard
The exfiltration mechanism is not clearly observable in the current dataset. Based on the recorded network communication, the submitted data appears to be sent back to the same page, with no indication of external channels. The observed web requests and source code show no evidence of Telegram, webhook or API based exfiltration, suggesting that data handling is stored locally within the web server.
Also, the registration process lacks effective input validation controls, allowing users to submit unverified or falsified information. For instance, the system allows the submission of fabricated identification documents during account creation.
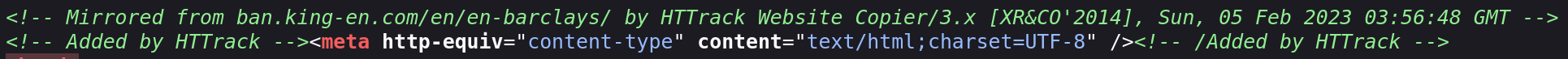
A section of the source code from the homepage.
A section of the source code from the login page.
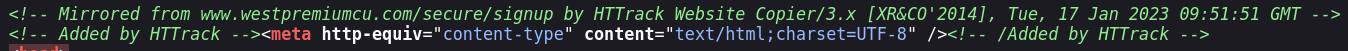
The phishing page source code indicates the use of the HTTrack website copier to replicate content from external pages, which are likely controlled by the same threat actor. This behaviour suggests a templated approach to infrastructure deployment, enabling rapid creation and reuse of phishing pages with minimal modification. Such tooling is commonly associated with lower sophistication phishing operations, where reliance on publicly available cloning utilities reduces development effort but also introduces identifiable artefacts. In contrast, more advanced phishing kits typically employ server-side rendering, dynamic content generation, or obfuscation techniques to hinder detection and attribution.
Fake courier-themed page
At first glance, the website appears to looks like a legitimate courier service, with each button leading to the same home page. However, upon closer inspection, it becomes evident that the pages are only for display purposes, as there are several evidence that the site lacks real functionality:
The provided contact details appear non-functional. The WhatsApp number is unregistered, and the email is invalid.
Source code analysis shows the site mirrors content from topexpresdelivery[.]com (last seen in 2020) and jetexpressdeliveries[.]com (last seen in 2023).
The tracking feature accepts any input but returns no results, indicating no input validation.
jetexpressdeliveries[.]com has an SSL certificate renewed on 20 March 2026 and has been flagged as untrusted multiple times since 24 July 2025.
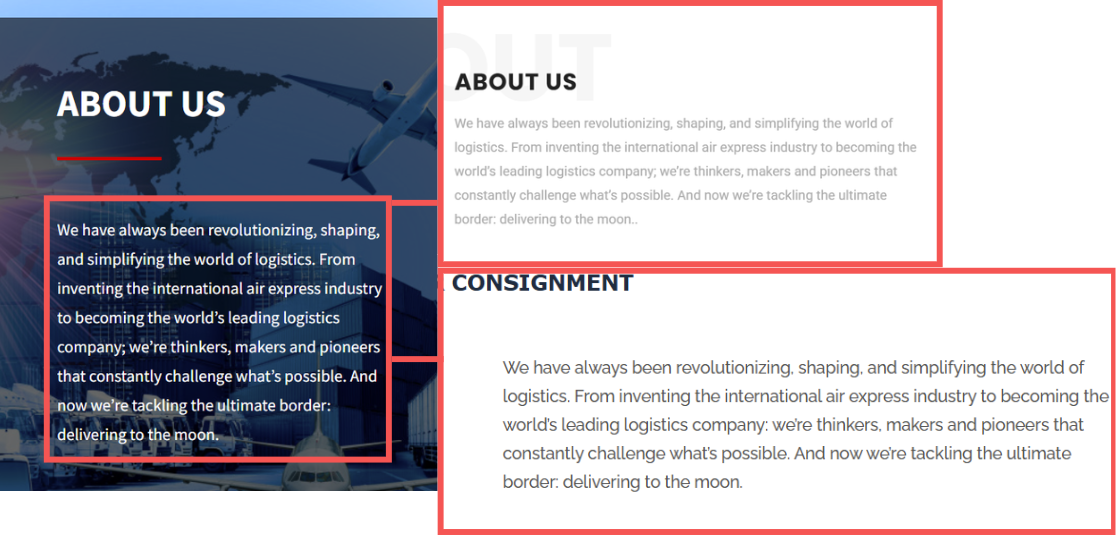
An additional observation indicates that the “About Us” section of jetexpressdeliveries[.]com is identical to that of two other courier-themed websites, expressguage[.]com and globalskydelivery[.]com. Both of these sites also appear to be fraudulent, with supporting indicators noted previously, dating back as early as 24 July 2025.
Comparison of the “About Us” content of multiple discovered courier-themed phishing page.
In summary, the delivery-themed websites examined are strongly suspected to be fraudulent. Analysis of their source code shows they were replicated using HTTrack, they contain identical “About Us” content, and the website features do not operate as intended.
The human layer aspect
This fraud case demonstrates deliberate exploitation of the human layer through trust-based pretexting and workflow manipulation. By impersonating a known overseas contact and introducing a plausible cross-border transaction, the attacker leveraged familiarity and business context to lower suspicion and initiate action. The subsequent use of a spoofed online banking site further capitalised on this trust, prompting the victim to perform purchase order under perceived legitimacy. As noted in public advisories, BEC actors “impersonate trusted entities to trick victims into making financial transactions or revealing sensitive information”, highlighting how such operations rely less on technical compromise and more on manipulating human trust, decision-making, routine, and urgency to achieve their objectives.
Infrastructure analysis
The observed infrastructure displays characteristics consistent with a phishing-as-a-service model. Infrastructure is distributed rather than centralised, with both IPv4 and IPv6 observed. This approach likely enhances resilience and complicates tracking. The use of infrastructure such as 198.251.89.82, the IP address of the Barclays Bank phishing page, alongside the broader hosting pattern, suggests reliance on virtual private server providers, potentially favouring low-cost or abuse-tolerant services to support rapid provisioning and rotation.
Overall, the scale, modularity, and hosting distribution support the assessment that this infrastructure forms part of a phishing-as-a-service ecosystem, although no direct attribution to a specific actor or marketplace has been identified.
Syntx’s observation
Several elements of the activity remain unconfirmed and require further investigation. The delivery vector is unknown, with possible delivery via email phishing, SMS phishing, or malvertising. The credential exfiltration mechanism is also unconfirmed, with no identified destination endpoints or evidence of Telegram, webhook, or API-based exfiltration. Attribution remains unclear, with no identified threat actor, group, or linkage to known phishing kit families. Victim targeting is similarly unconfirmed, with no clear geographic or sector-specific focus beyond courier and banking themes.
Analytical hypotheses suggest that delivery-themed domains may act as the initial lure, supporting a staged flow consistent with phishing campaigns. Banking domains are likely used for credential harvesting, given the presence of login forms. The use of a CAPTCHA stage prior to authentication may indicate anti-analysis and filtering measures. The scale of infrastructure, including a high volume of structurally similar pages and reusable templates, may indicate a phishing-as-a-service ecosystem, although no direct linkage has been identified.
Mitre Att&ck mapping
| Impact | Technique | ID | Description |
|---|---|---|---|
| Reconnaissance | Search Open Websites/Domains | T1593 | Adversary identifies professional associations to build a credible "known contact" persona. |
| Initial Access | Phishing | T1566.002 | Initial contact via social/messaging using a trusted pretext to deliver the first malicious request. |
| Execution | User Execution: Malicious Link | T1204.001 | Victim is manipulated into clicking URLs that lead to adversary-controlled infrastructure. |
| Credential Access | Input Capture | T1056 | A clone of the Barclays homepage used to capture user-entered credentials and authentication details. |
| Defense Evasion | Masquarading | T1036 | Use of a fake logistics/tracking portal to masquerade as a legitimate service and reinforce the fraud narrative. |
| Impact | Financial Theft | T1657 | Initial contact via social/messaging using a trusted pretext to deliver the first malicious request. |
Indicators of Compromise (IOCs)
| IoC | Description |
|---|---|
| hxxps://bnk[.]ing-boa[.]pro/en/en-bclys/ | Barclays Bank phishing page |
| hxxps://jetexpressdeliveries[.]com/ | Courier phishing page |
| ing-boa[.]pro | Domain |
| jetexpressdeliveries[.]com | Domain |
| 198[.]251[.]89[.]82 | IP address |
| 46[.]202[.]172[.]167 | IP address |
| www.westpremiumcu[.]com/secure/signup/ | Cloned for registration page |
| www.westpremiumcu[.]com/secure/ | Cloned for login page |
| hxxps://barcl.ays-uk[.]com/en/en-barclays/ | Linked to the phishing page |
Recommendations
User Awareness Educate employees and customers on staged phishing tactics, including fraudulent banking and delivery lures, and encourage verification of sender and domain authenticity.
Domain Monitoring Track and block high-risk domains, particularly newly registered or recently renewed sites mimicking legitimate services.
Multi-Factor Authentication Enforce MFA for all critical accounts to reduce risk if credentials are compromised.
Technical Controls Use URL filtering, web isolation, and phishing detection tools to block access to fraudulent pages and staged login flows.
Threat Intelligence Monitor phishing kit patterns, infrastructure reuse, and hosting behaviour, and share relevant indicators to strengthen situational awareness.