GhostCargo, a 5-years campaign
TLDR;
GhostCargo is a 5+ year fraud operation running fake bank portals and fake delivery sites, with at least 13 scam domains across six fraud verticals on a single bulletproof server
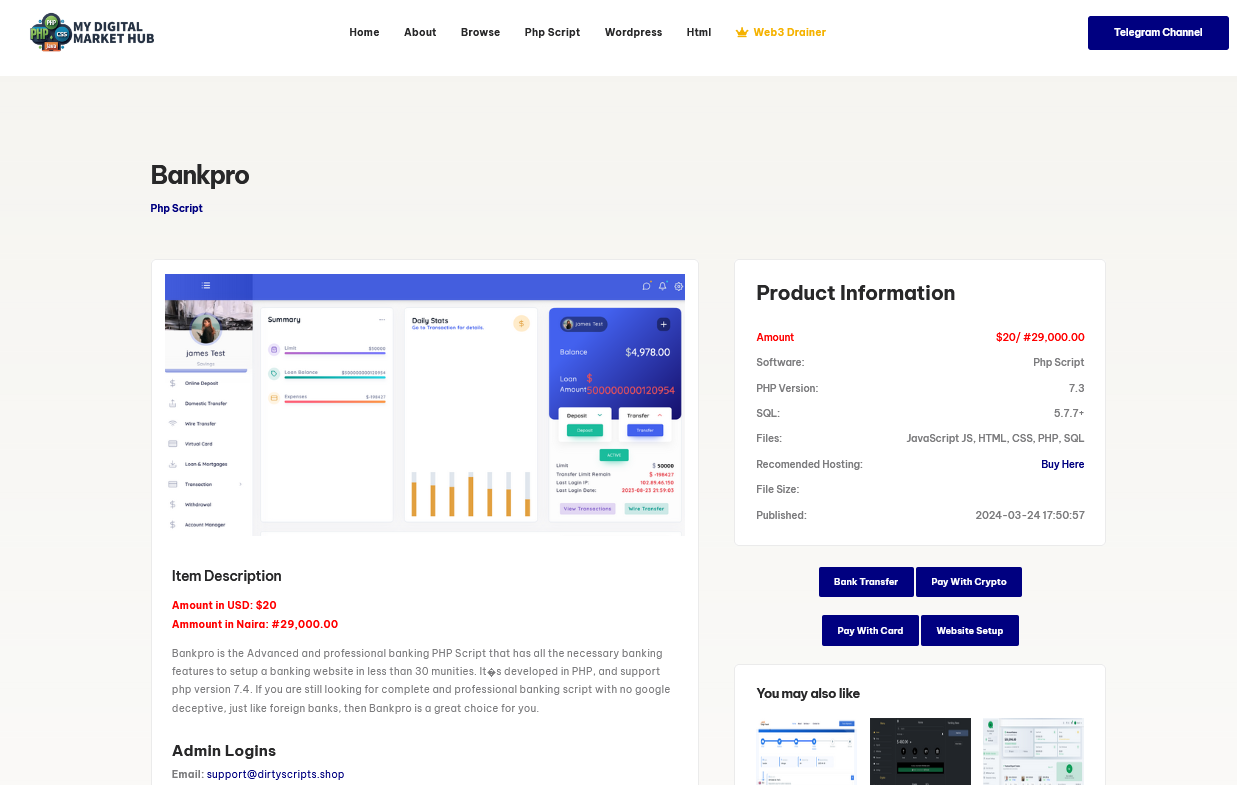
The fake banking sites run "Bankpro", a $20 commercial phishing kit traced to a developer in Lagos, Nigeria (codename: DirtyMill), with 700+ detections across 41+ domains globally
The actor is not a developer: they scrape templates, buy off-the-shelf kits, and outsource web development. A shared Google Analytics property links the delivery front to an external web developer
Infrastructure has evolved from mainstream hosting (Hostinger) to abuse-resistant bulletproof hosting (FranTech/BuyVM), with DNS, web, and mail self-hosted on a single VPS
The operator remains unidentified. Open-source investigation continues in parallel
Recap: What We Know
In our first report, we identified bnk.ing-boa[.]pro as a fake Barclays Bank phishing portal used to defraud a Malaysian victim of more than RM50,000. The site was built from scraped templates, hosted on bulletproof infrastructure, and operated with a companion fake logistics site (jetexpressdeliveries[.]com) to add legitimacy. We call this campaign GhostCargo.
How the Scam Worked
The GhostCargo scam chain combines social engineering, phishing infrastructure, and fabricated logistics to defraud victims. Initial contact comes through an acquaintance in Australia, who introduces the victim to their “friend” (the TA) presented as a business owner looking to purchase goods from Malaysia. The TA then builds credibility through sustained pretexting and persuasion, eventually asking the victim to arrange purchases via a supplier “based in Sabah” (a fake company), with the goods supposedly destined for Venezuela.
To execute the payment, the TA shares access to an online banking portal that mimics Barclays (bnk.ing-boa[.]pro) and provides “login details” so the victim can complete the transaction to the fake supplier. When the TA later demands shipment tracking proof, the victim requests documentation from the supplier, who responds with a fake tracking website (e.g., jetexpressdeliveries[.]com) populated with fabricated shipment data. The TA then repeats the same pressure cycle, pushing a further purchase (this time tied to an Indonesia-based supplier) with the victim only realising the scam after losses confirmed at over RM50,000.
Key Takeaways from our first report
Phishing site built using HTTrack-scraped templates from older phishing campaigns
Infrastructure on FranTech (PONYNET) AS53667, “bulletproof hosting”
Victim PII, photo ID, and wire transfer details all collected by the portal
Amateur server config: public file uploads, missing security headers, broken CAPTCHA
Expanding the Picture
Following analysis of the primary targets, we examined the shared hosting environment to identify other domains operated by the same actors. The IP 198.251.89[.]82 hosts 13 scam domains under a single DirectAdmin account, all sharing the same nameservers. Three of these share enough technical and operational signatures with GhostCargo to be attributed to the same actor with high confidence.
Common Signatures Across the Cluster
| Hosting provider | FranTech Solutions (AS53667), Cheyenne WY |
| IP address | 198.251.89[.]82 |
| Nameservers |
ns115.my-control-panel[.]com ns116.my-control-panel[.]com |
| Web server | LiteSpeed + DirectAdmin |
| Phishing kit | Dirty Scripts Bankpro |
| Kit default credentials | support@dirtyscripts[.]shop / 12345678 |
| Cert behaviour | Wildcard certs via Let's Encrypt, Sectigo, Google Trust |
| CAPTCHA | Custom slide CAPTCHA |
The cluster includes both fake bank portals and fake logistics/courier sites, a consistent pattern across all high-confidence same-actor domains. The combination of a fake bank and a fake delivery front is the core social engineering structure of GhostCargo.
The Infrastructure
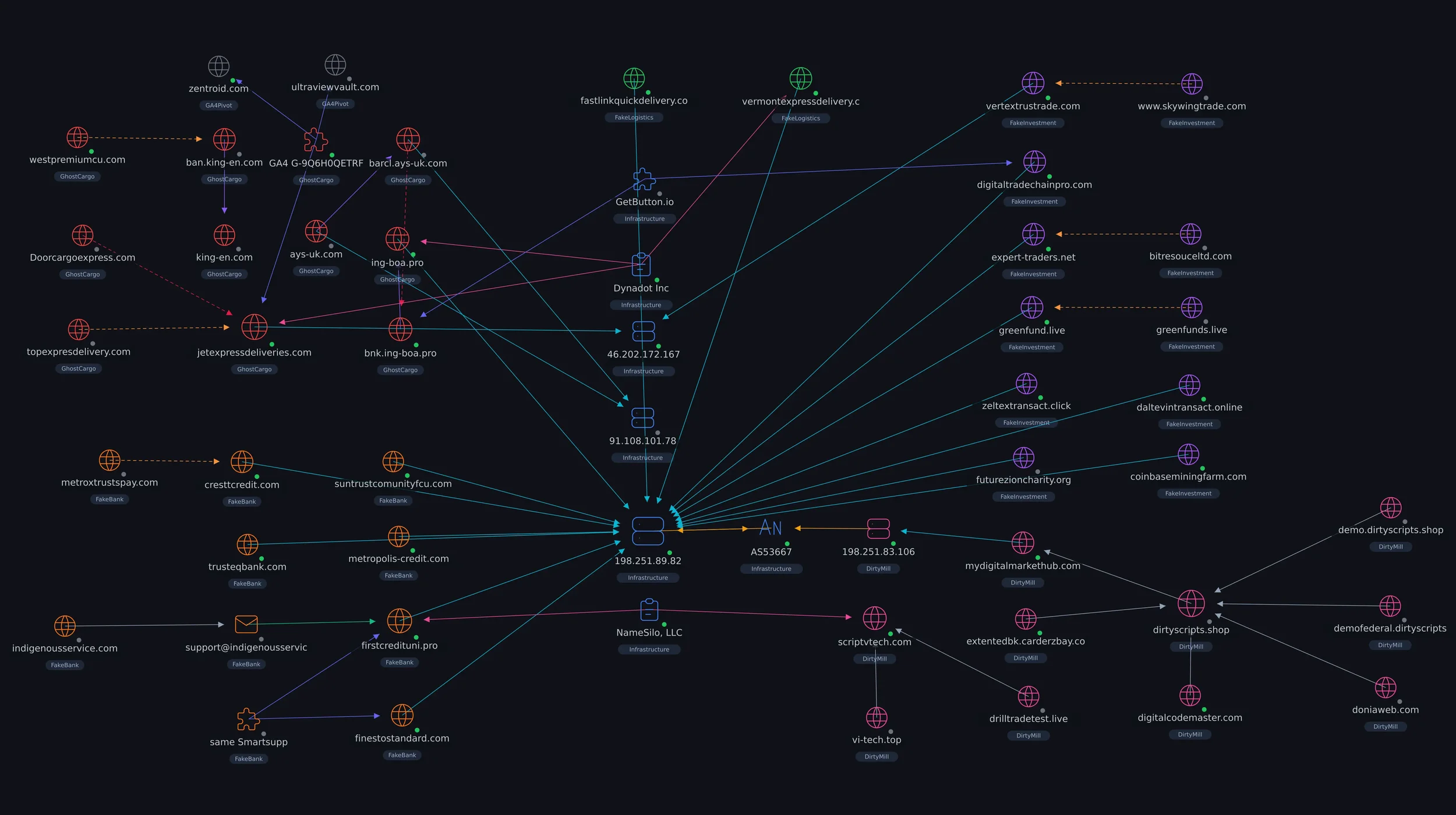
The overall infrastructure
The graph above maps the full infrastructure uncovered across this investigation, relationships spanning three distinct clusters. The picture that emerges is not a single phishing site but a multi-year, multi-vertical fraud operation backed by a commercial phishing kit supply chain.
The most immediate observation is density. The majority of domains resolve to a single IP address, 198.251.89[.]82, hosted on FranTech (AS53667) bulletproof infrastructure in Cheyenne, Wyoming.
A second, smaller cluster sits on Hostinger infrastructure in Paris. Both clusters are linked by shared naming patterns, shared registrars, and confirmed use of the same Dirty Scripts Bankpro phishing kit.
The following subsections break down each cluster in detail.
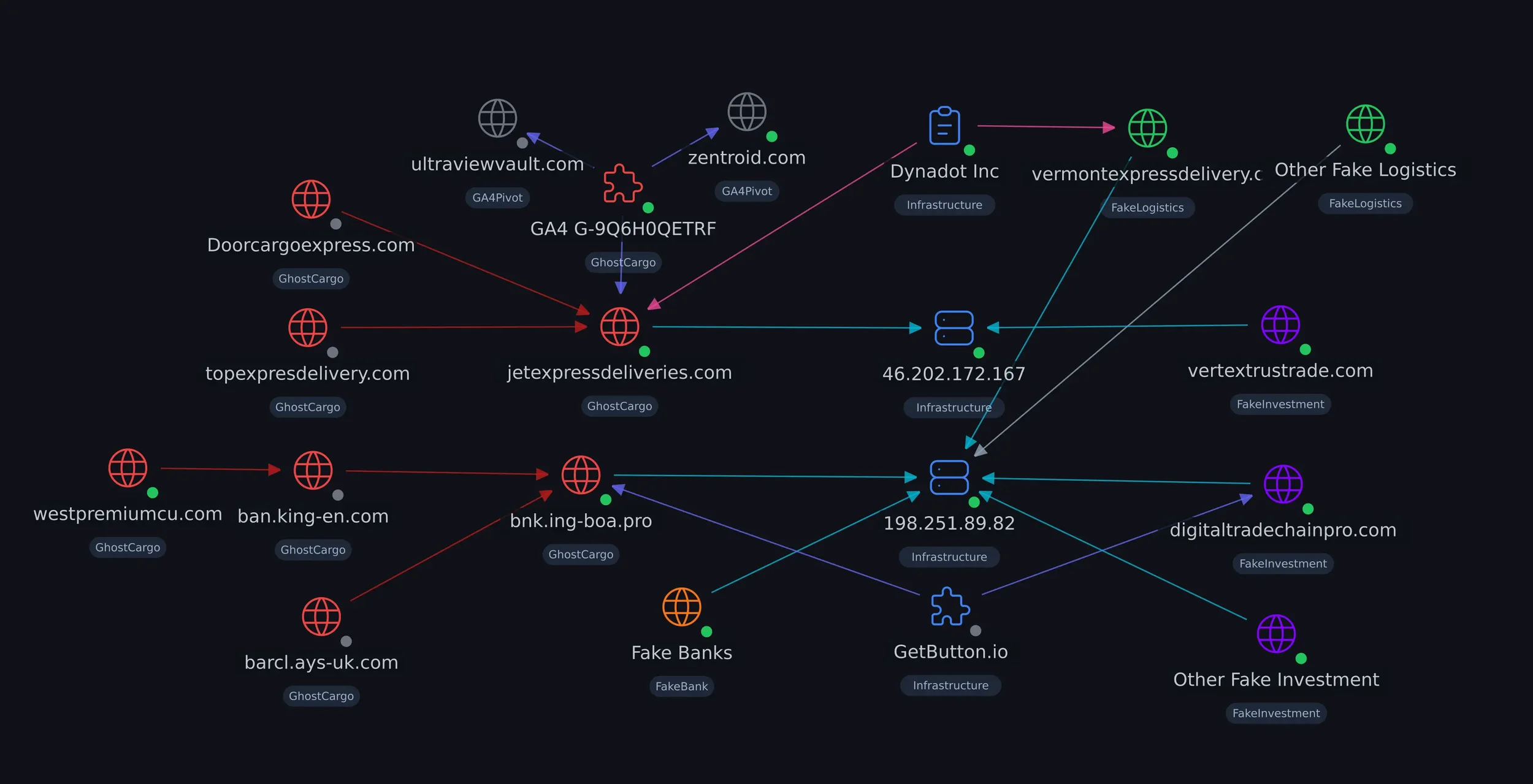
Cluster: GhostCargo
The GhostCargo cluster centres on
bnk.ing-boa[.]pro (fake Barclays portal) and jetexpressdeliveries[.]com (fake logistics front). Both trace back through confirmed predecessor domains: the bank portal through barcl.ays-uk[.]com, ban.king-en[.]com, and westpremiumcu[.]com;
the delivery front through topexpresdelivery[.]com and Doorcargoexpress[.]com. The actor has been iterating on both fronts since at least September 2020.
The two active sites sit on separate hosting providers: FranTech bulletproof hosting for the bank portal, Hostinger shared hosting for the delivery front. The split appears deliberate, placing the credential harvesting site on abuse-resistant infrastructure while keeping the less sensitive logistics front on cheaper hosting.
In the graph, both IPs act as hub nodes, connecting GhostCargo's core domains outward to the co-hosted scam sites through shared hosting, registrars, and web widgets (e.g. GetButton.io).
The strongest attribution lead is Google Analytics property G-9Q6H0QETRF, found on jetexpressdeliveries[.]com and two unrelated sites: an Indian 3D design company and an IPTV piracy reseller. A single GA4 property shared across three unconnected sites points to a common web developer. This is the most actionable pivot for identifying the GhostCargo operator.
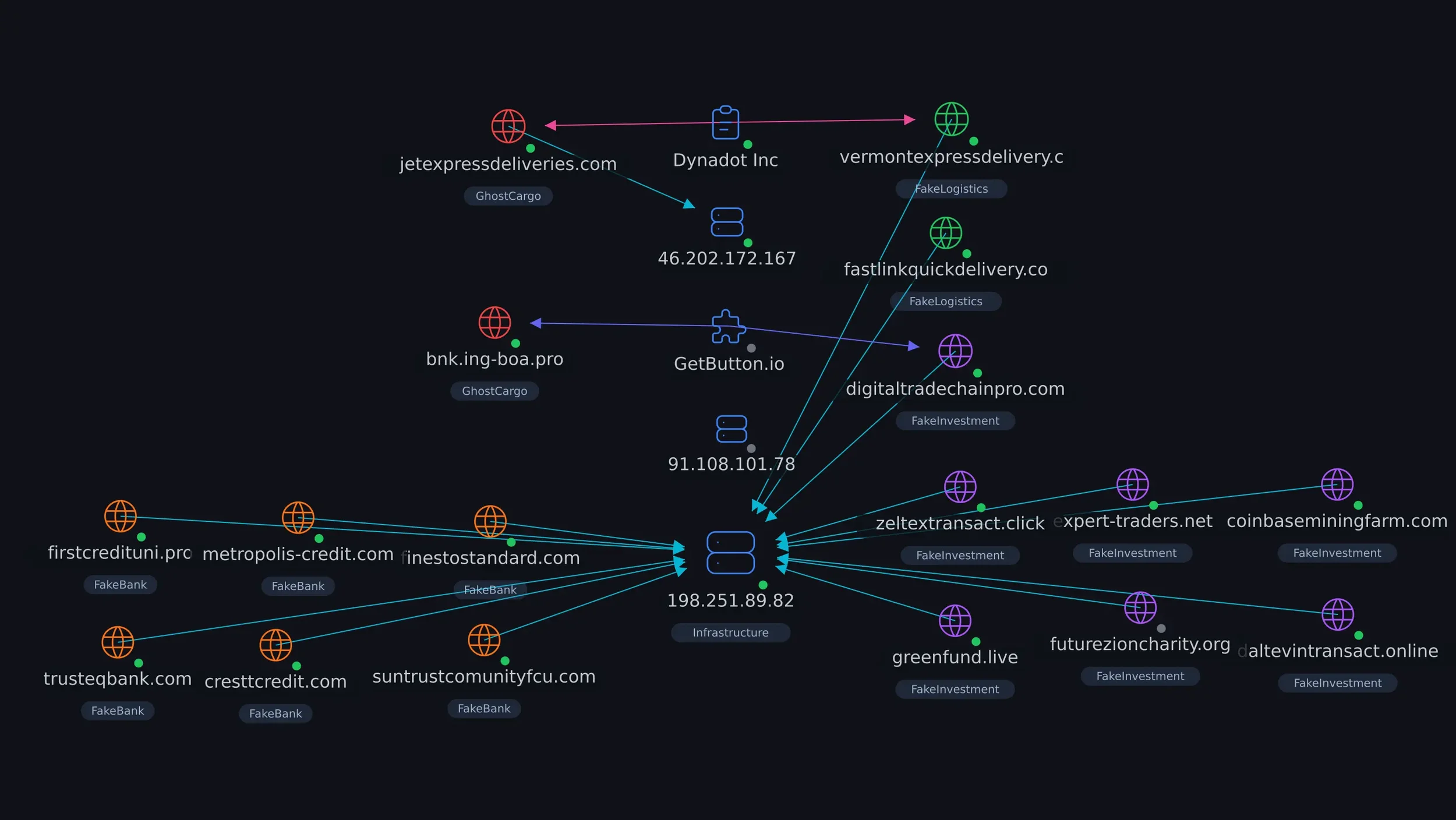
Cluster: Co-hosted Scam Domains
Thirteen additional scam domains share the same IP, nameservers, and DirectAdmin hosting account as bnk.ing-boa[.]pro. This is not coincidental co-location; the matching nameservers confirm they are managed from the same control panel.
The domains span at least six fraud verticals: fake banks (e.g. firstcredituni[.]pro, suntrustcomunityfcu[.]com), fake delivery services, fake trading platforms, crypto scams, fake charities, and fake transaction services.
Three are attributed to GhostCargo with high confidence based on shared naming patterns, the uncommon .pro TLD, and the same Dynadot registrar as the core GhostCargo domains.
The fake banking sites in this cluster all run “Dirty Scripts Bankpro”. The same kit, the same hosting, the same admin panel. Whether this is one actor running every vertical or a small group sharing a single VPS, the operational footprint is unified.
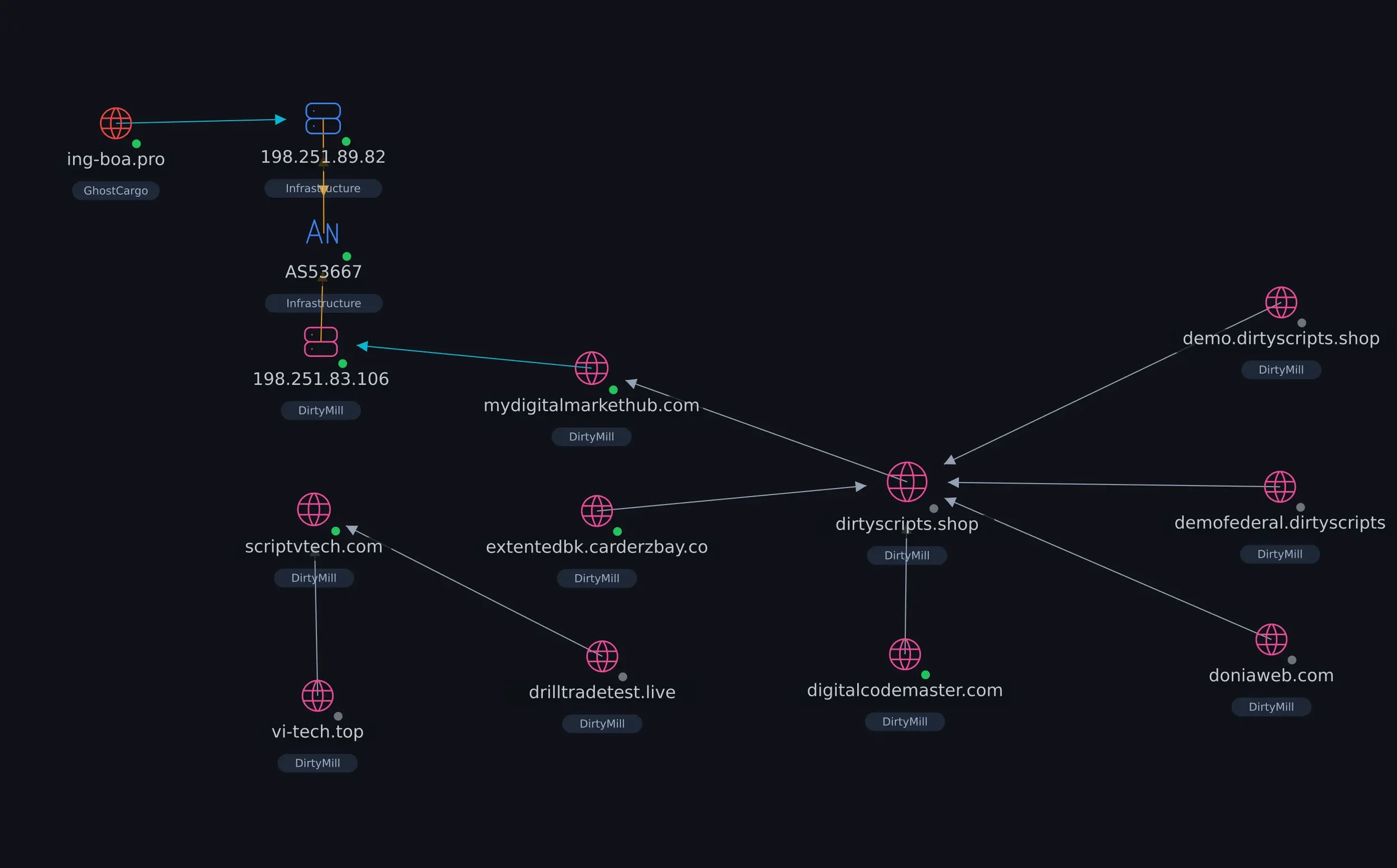
Cluster: Kit Supply Chain
This cluster maps the supply side: the “Dirty Scripts Bankpro” phishing kit and its distribution network. It does not share many direct infrastructure links with the other two clusters, and that is besides the point. The relationship between GhostCargo and DirtyMill is supplier-to-customer, visible through kit fingerprints rather than network edges.
The cluster includes marketplaces (e.g. scriptvtech[.]com), demo servers, and third-party distribution through forums. One infrastructure edge does cross over: a marketplace mirror sits on the same FranTech ASN as the scam domains, though on a different IP and control panel.
The kit has been detected more than 700 times on urlscan.io across 41+ unique domains globally. GhostCargo is one deployment among many. Understanding this supply chain is key to understanding how the operation scales, and why the GhostCargo operator is likely a customer, not the kit developer.
Enter DirtyMill
We use the codename "DirtyMill" to refer to the kit supply chain behind GhostCargo's fake banking infrastructure. The phishing portal at bnk.ing-boa[.]pro runs "Bankpro", a commercial PHP phishing kit sold for $20 under the brand "Dirty Scripts". The kit was identified through default page titles left unchanged by the operator (e.g. "Dirty Scripts - Login" on firstcredituni[.]pro) and confirmed through JavaScript stack fingerprinting against the official demo server.
The script named Bankpro closely resembles a legitimate financial platform called BankPro, suggesting the threat actor may be leveraging the brand’s recognition, although coincidence cannot be ruled out.
The link between GhostCargo and Bankpro is fingerprint-based, not a direct branding match. The co-hosted site firstcredituni[.]pro is a confirmed default Bankpro deployment, with "Dirty Scripts" branding still visible in page titles and an identical JavaScript stack to the official demo server.
The primary portal bnk.ing-boa[.]pro is more heavily customized:
the operator stripped all kit branding,
restructured directory paths, swapped jQuery versions,
and added a slider CAPTCHA.
However, three Bankpro-specific code artifacts remain in bnk.ing-boa[.]pro (the misspelled pw_strenght.js filename, the survey_func.js obfuscation pattern, and the verify_captcha.php endpoint that accepts empty POST requests). These fingerprints do not appear in any other known kit or public library.
Bankpro is designed for full identity theft and wire fraud. It collects credentials, SSNs, photo IDs, and wire transfer details through a multi-step registration flow, and ships with an admin panel, anti-forensic JavaScript, and a fake CAPTCHA that performs no actual validation.
Bankpro toolkit listing in storefront, with links to demo site
The screenshot above shows Bankpro's product listing on mydigitalmarkethub[.]com, one of the developer's own storefronts. The listing includes preview screenshots of the kit's admin dashboard and victim management panel, the $20 price point, default admin credentials, and an item description advertising it as an "online banking PHP Script built for the enterprise banking experience". The listing was captured before it was removed from the marketplace in April 2026.
DirtyMill at a Glance
| Kit name | Bankpro (by Dirty Scripts) |
| Price | $20 USD / 29,000 NGN |
| Primary marketplace | scriptvtech[.]com (Moscow VPS, reg. 2019) |
| Secondary marketplaces | mydigitalmarkethub[.]com (FranTech AS53667), digitalcodemaster[.]com |
| Forum distribution | DoniaWeB (336 downloads), carderzbay[.]com |
| Global deployments | 762 detections on urlscan.io, 41+ unique domains |
| Kit variants | Bankpro, Federal Bank, Union, Simple, Credixa Bank Pro |
| Developer location | Ikeja, Lagos, Nigeria |
| Developer handles | Vtech12 (Facebook), VtechnologyInc (Telegram), mydigitalmarkethub (email/WhatsApp) |
| Default admin creds | support@dirtyscripts[.]shop / 12345678 |
The developer operates at least three interconnected storefronts selling identical products with shared demo infrastructure. The marketplaces are linked through cross-referenced demo credentials (e.g. support@dirtyscripts[.]shop used on scriptvtech[.]com listings), shared seller profiles, and overlapping product catalogues. The developer's location is confirmed through converging indicators:
a Lagos address on scriptvtech[.]com,
a Nigerian phone number, Paystack (Nigerian payment gateway) integration
NGN pricing, and a Yoruba name used in demo accounts.
Beyond banking kits, the marketplace sells courier tracking scripts (e.g. "Cargoy" at $100), crypto wallet drainers ($250-$500), military romance scam tools, fake visa applications, and fake document generators. This is not a one-product shop. It is a full-service fraud toolkit supplier, and its product catalogue maps directly to GhostCargo's operational needs: a fake bank and a fake delivery tracker.
The Supply Chain: GhostCargo and DirtyMill
GhostCargo is a customer of DirtyMill. The Bankpro kit fingerprint is confirmed in bnk.ing-boa[.]pro through three code artifacts that do not appear in any other known kit or public library. The co-hosted site firstcredituni[.]pro is a stronger match, still running default Bankpro branding ("Dirty Scripts - Login" in the page title) with an identical JavaScript stack to the official demo server.
There is not enough evidence to attribute the two operations to the same actor.
DirtyMill operates as a commercial kit supplier, selling low-cost PHP scripts through multiple storefronts with indicators pointing to a West African developer.
GhostCargo is an end-user deployment with at least one confirmed victim in Malaysia, using Australian and UK VoIP numbers and a fake logistics front. The infrastructure and operational patterns do not overlap in ways that would suggest a single operator. Based on what we have, the most likely relationship is supplier to customer.
The kit was available for as little as $20 on mydigitalmarkethub[.]com, or free via forum redistribution on DoniaWeB (336 downloads). There is no way to determine which channel GhostCargo used to obtain it.
Five Years of GhostCargo
The earliest confirmed GhostCargo infrastructure dates to September 2020. Since then, the actor has cycled through at least six domains across two parallel tracks (fake banks and fake delivery fronts), moved between hosting providers, and shifted from HTTrack-scraped templates to a commercial phishing kit. There has been no confirmed law enforcement action during this entire period.
The timeline below is reconstructed from certificate transparency logs, HTTrack watermark dates, urlscan captures, and direct site observation. Where exact dates are available (from certificates), they are used. Where only a month is known (from HTTrack timestamps or first urlscan appearance), the first of the month is used as an approximation.
| Date | Event | Domain / IOC |
|---|---|---|
| 2020-09-01 | Earliest predecessor delivery site deployed | topexpresdelivery[.]com |
| 2020-12-01 | Wildcard cert issued; earliest confirmed bank infrastructure | king-en[.]com |
| 2023-01-01 | Template scraped from legitimate US credit union | westpremiumcu[.]com (source) |
| 2023-02-01 | Bank portal cloned from scraped template | ban.king-en[.]com |
| 2023-02-01 | Delivery front deployed; tracking page cloned from predecessor | jetexpressdeliveries[.]com |
| 2024-06-15 | Previous Barclays portal active on Hostinger | barcl.ays-uk[.]com |
| 2025-08-02 | New domain registered; portal built from barcl.ays-uk[.]com template | bnk.ing-boa[.]pro |
| 2025-11-01 | Home page refreshed with updated branding | bnk.ing-boa[.]pro |
| 2026-02-01 | Wildcard cert issued; additional subdomains likely | *.ing-boa[.]pro |
| 2026-04-07 | Confirmed active and collecting victim data | bnk.ing-boa[.]pro |
Two patterns stand out.
First, the actor maintains parallel infrastructure: a fake bank and a fake delivery front running simultaneously, hosted on different providers.
Second, the transition from barcl.ays-uk[.]com (Hostinger shared hosting) to bnk.ing-boa[.]pro (FranTech bulletproof hosting) shows the actor moving toward more abuse-resistant infrastructure over time.
The three-month gap between the predecessor going offline (May 2025) and the new domain appearing (August 2025) suggests a deliberate migration, not a rushed response to a takedown.
GhostCargo Attribution
The identity of the GhostCargo operator remains unknown. What follows is an assessment of what the infrastructure and operational patterns suggest about the actor, and where the strongest leads point.
Not geography-specific
The confirmed victim is Malaysian, but the broader infrastructure does not point to a single target region. Co-hosted domains impersonate US credit unions, use US and UK fake addresses, and the actor's phone numbers span four countries (Australia, UK, US, with at least one rotated out over time). The six fraud verticals across 13+ co-hosted domains suggest an actor who runs parallel campaigns tailored to different regions, not one fixed on Southeast Asia.
Not a developer
Five years of consistent tool reuse: HTTrack scrapes (2020-2023), a commercial Drupal theme for the delivery front, and a $20 Bankpro kit for the bank portal.
No evidence of custom code.
The GA4 property G-9Q6H0QETRF shared across jetexpressdeliveries[.]com and two unrelated sites (zentroid[.]com, ultraviewvault[.]com) suggests the actor outsourced web development to someone who reused their own analytics account across client projects.
Improving opsec over time
The actor migrated from Hostinger shared hosting (barcl.ays-uk[.]com, 2024) to FranTech/BuyVM bulletproof hosting (bnk.ing-boa[.]pro, 2025). FranTech (AS53667) is documented in threat intelligence as abuse-tolerant.
The current setup self-hosts DNS, web, and mail on a single VPS with nameservers on the same IP, leaving no external provider to file abuse reports with. The delivery front still sits on Hostinger, suggesting a deliberate split: credential harvesting on bulletproof infrastructure, less sensitive fronts on cheaper providers.
What Defenders and Public can do
For threat intelligence teams
The Bankpro kit fingerprints documented in this report (pw_strenght.js, survey_func.js with _0xb44ax* obfuscation, verify_captcha.php returning success on empty POST) have no prior public documentation. These can be used to detect other Bankpro deployments beyond the 41+ domains already identified on urlscan. The kit's 762 detections suggest a much larger deployment footprint than what this investigation has covered.
For hosting and domain providers
The IOC list at the end of this report includes all confirmed domains, IPs, and nameservers. FranTech (AS53667) hosts the primary infrastructure. Dynadot is the registrar for the .pro domains. Certificate authorities (Let's Encrypt, Sectigo, Google Trust Services) have issued certs for confirmed phishing domains.
For the public
GhostCargo campaigns follow a recognisable pattern: initial contact via WhatsApp from a foreign number, a business partnership pretext involving commodity trading or chemical supplies, a request to make a payment "on behalf of" the actor, then redirection to a fake bank portal and a fake delivery tracking site. If you or someone you know has been approached with this pattern, report it to local police and your bank immediately. Do not enter credentials on any site you were directed to via WhatsApp.
Conclusion
GhostCargo is not an isolated scam. It is one deployment within a larger fraud ecosystem: a five-year-old operation spanning at least 13 scam domains across six fraud verticals, backed by a $20 commercial phishing kit and hosted on bulletproof infrastructure designed to resist takedown. The confirmed victim loss of RM50,000+ is a floor, not a ceiling.
This investigation has mapped 54 nodes of technical infrastructure across three clusters, identified the kit supply chain (DirtyMill, 762 detections across 41+ domains globally), documented a direct predecessor site with potentially recoverable hosting records, and surfaced a credible attribution lead through a shared Google Analytics property. The actor is not sophisticated, but they are persistent: five years of operation, improving opsec, and no confirmed law enforcement action.
The identity of the GhostCargo operator remains the central open question. Three law enforcement requests (Google, Smartsupp, and Hostinger) represent the clearest path to unmasking them. Pending those, open-source investigation can continue: WHOIS lookups on predecessor domains, phone number cross-referencing, subdomain enumeration against the February 2026 wildcard certificate, and monitoring urlscan for new Bankpro deployments using the kit fingerprints documented here. Every new deployment that surfaces is another chance to find an operator who made a mistake the GhostCargo actor has so far avoided.
IOCs
GhostCargo Core
| IOC | Type | Notes |
|---|---|---|
| bnk.ing-boa[.]pro | Domain | Active fake Barclays portal |
| ing-boa[.]pro | Domain | Parent domain; wildcard cert *.ing-boa[.]pro issued Feb 2026 |
| jetexpressdeliveries[.]com | Domain | Fake logistics front (Drupal + transpix theme) |
| barcl.ays-uk[.]com | Domain | Predecessor Barclays portal (Jun 2024 to May 2025, now NXDOMAIN) |
| ays-uk[.]com | Domain | Parent of predecessor; same Hostinger IP |
| ban.king-en[.]com | Domain | Predecessor bank portal (Feb 2023, now NXDOMAIN) |
| king-en[.]com | Domain | Parent domain; wildcard cert from Dec 2020 |
| topexpresdelivery[.]com | Domain | Predecessor delivery domain (Sep 2020, HTTrack source) |
| Doorcargoexpress[.]com | Domain | Predecessor tracking page template (Feb 2023) |
High-Confidence Same-Actor Domains
| IOC | Type | Notes |
|---|---|---|
| vermontexpressdelivery[.]com | Domain | Fake delivery; same NS, IP, registrar |
| fastlinkquickdelivery[.]com | Domain | Fake delivery; same NS, IP, registrar |
| firstcredituni[.]pro | Domain | Fake bank; confirmed Bankpro default deployment, .pro TLD match |
Co-hosted Scam Domains (same IP, same NS)
| IOC | Type | Notes |
|---|---|---|
| suntrustcomunityfcu[.]com | Domain | Fake credit union |
| cresttcredit[.]com | Domain | Fake credit institution |
| trusteqbank[.]com | Domain | Fake bank |
| metropolis-credit[.]com | Domain | Fake credit |
| finestostandard[.]com | Domain | Fake financial institution |
| digitaltradechainpro[.]com | Domain | Fake trading platform |
| expert-traders[.]net | Domain | Fake trading |
| coinbaseminingfarm[.]com | Domain | Coinbase impersonation / crypto scam |
| greenfund[.]live | Domain | Fake charity / investment |
| futurezioncharity[.]org | Domain | Fake charity |
| daltevintransact[.]online | Domain | Fake transaction service |
| zeltextransact[.]click | Domain | Fake transaction service |
| hiltonacessglobal[.]com | Domain | Fake Hilton access / global services |
| zenixtransit[.]online | Domain | Fake transit / logistics |
| royalgatesschools[.]com | Domain | Fake school with finance admin portal |
| credixrise[.]com | Domain | Fake banking (Cloudflare NS, same IP) |
Infrastructure
| IOC | Type | Notes |
|---|---|---|
| 198.251.89[.]82 | IP | Primary hosting IP (FranTech AS53667, Cheyenne WY) |
| 91.108.101[.]78 | IP | barcl.ays-uk[.]com hosting IP (Hostinger, Paris) |
| 46.202.172[.]167 | IP | jetexpressdeliveries[.]com hosting IP (Hostinger) |
| AS53667 | ASN | FranTech Solutions (PONYNET), bulletproof hosting |
| ns115.my-control-panel[.]com | Nameserver | Hosted on same IP as scam domains |
| ns116.my-control-panel[.]com | Nameserver | Hosted on same IP as scam domains |
| G-9Q6H0QETRF | GA4 ID | On jetexpressdeliveries[.]com; shared with zentroid[.]com and ultraviewvault[.]com |
Actor Contact Points
| IOC | Type | Notes |
|---|---|---|
| +61 488 834 796 | Phone | Actor lure number (Australian VoIP) |
| +44 7300 945231 | Phone | Actor WhatsApp on jetexpress (UK VoIP) |
| +1 325 632 8510 | Phone | Actor phone, US Texas (decommissioned) |
| +1 484 983 2135 | Phone | Actor phone, vermontexpress (US Pennsylvania) |
| +1 929 399 3571 | Phone | Actor phone, firstcredituni (US NYC) |
| admin@ing-boa[.]pro | Operator contact | |
| support@indigenousservice[.]com | Contact email on firstcredituni[.]pro |
Kit Detection Fingerprints
| IOC | Type | Notes |
|---|---|---|
| pw_strenght.js | Code fingerprint | Bankpro-specific misspelled filename |
| survey_func.js / _0xb44ax* | Code fingerprint | Bankpro registration wizard obfuscation pattern |
| verify_captcha.php | Code fingerprint | Returns {"success":true} on empty POST body |
| support@dirtyscripts[.]shop / 12345678 | Default credential | Bankpro kit default admin login |